Further to the adoption of the GDPR, and as businesses are rolling out new tools and mechanisms to carry out operations, the question arises often whether these operations are GDPR compliant. Does access to systems that contain personal data have to be verified by two-factor authentication? Do customer databases always have to be pseudonymised? Do drives have to be permanently encrypted?
The obligations contained in the GDPR seemingly set a high bar for businesses to put in place compliant security measures. However, the guidance papers issued by ENISA (“Handbook on Security of Personal Data Processing”, December 2017), the French data protection authority (CNIL) (“Security of Personal Data”, 2018) and the Article 29 Working Party (“Guidelines on DPIA”, October 2017) shed some light on the minimum security measures that are expected from businesses when they handle personal data in general, sensitive personal data or data of a highly personal nature.
- Common errors committed when assessing and remedying security risks
When evaluating risks to personal data or systems, companies tend to assume that the absence of a security measure constitutes a valid parameter to determine risk, regardless of whether or not the measure in question is actually necessary to address a risk. Accordingly, the risk levels are possibly flawed or skewed.
Furthermore, because the absence of a security measure is often found by companies to constitute a “risk”, it will always have to be “fixed” by implementing a security measure, regardless of the actual risk level. For example, the absence of pseudonymised or encrypted personal data will lead companies to think that they need to implement both pseudonymisation and encryption measures, even if risk scores and the size of the personal data at risk are low.
- The challenge of evaluating risks and implementing appropriate security measures
Risks should be identified and measured as the likelihood of materialisation of a threat against the impact of such threat on privacy. ENISA, the CNIL and the EU data protection authorities refer to the following sequential steps that are necessary to carry out an assessment and recommendation on security of personal data:
- Step 1: Defining the processing operation (e.g., understanding the data processing operation, the kinds of personal data processed).
- Step 2: Understanding and evaluating the impact (e.g., minor inconveniences if disclosure, or major, significant and irreversible consequences).
- Step 3: Defining the possible threats (e.g., data loss, leaks, broad accessibility, etc.).
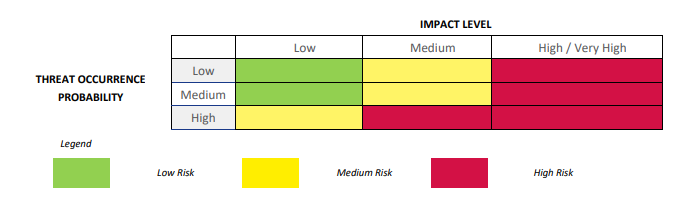
- Step 4: Evaluating risks, measuring threat levels against impact levels, e.g.:
- Step 5: Adopting the appropriate security measures to address the risks.
As can be seen, particularly in Steps 4 and 5, every security measure should address a risk, but the absence of a security measure does not in itself represent an issue, unless a risk is exposed and not addressed.
- Finding the appropriate security measure to address risks
The question then becomes, what security measures should be adopted by entities in order to address risks?
If risk levels are based on (a) the threat score and (b) the number of personal data infringement score, companies can opt to rely on this data to filter and focus on the higher-risk scores (i.e., larger amounts of personal data, potentially sensitive, being processed and subject to high levels of threat), and apply the general rules indicated by ENISA or CNIL.
For example, if the number of personal data infringement score (b) assigned to a certain system is low, then the absence of certain security measures should not be an obstacle to address that risk through other less onerous measures.
By contrast, there might be a need to implement a security measure if it is necessary to address a (high) risk. For example, if the level of risk is high, then one might need to implement appropriate (and even, to a certain extent, overlapping) security measures to ensure that the high level of risk is addressed.
ENISA and CNIL have provided the following categorisation of risk levels for the following types of personal data processes:
- Low-risk (low threat
and low impact):
- Marketing and advertising information (e.g., contact information such as name, postal address, telephone number, email).
- Contact details of B2B suppliers of services and goods (e.g., first and last name, contact information, tax and banking information (for suppliers)).
- Medium-risk
(low/medium threat and low/medium impact):
- Payroll processing information (e.g., social security number, taxation identifiers, date of employment, salary information).
- Recruitment data (e.g., academic education and qualifications, working experience, further professional or academic training , family status, first and last name, address, telephone numbers, date of birth, interview notes/report).
- Employee evaluation information (e.g., position within the SME, date of employment, employment history, technical skills, knowledge and behaviour).
- E-learning platform information (e.g., date of birth, date of admission, selected courses, evaluation results, grades).
- High-risk (medium/high
threat and medium/high impact):
- Health services data (e.g., social insurance number, medical examination results, pathologies, allergies, diagnosis and cure schemas, related administrative and financial information).
As can be seen, only in very specific data processes might the systems be exposed to high risks. In other cases which might concern personal data such as salary information or education, the level of risk is medium or even low. This will have a bearing on the security measures that are necessary to address each purpose.